This website uses cookies to ensure you get the best experience on our website. Learn more
Articles written by Marcus White
-
May
23

Guide to the PCI-DSS v4.0.1 regulations [Updated for 2025]
The PCI DSS compliance framework has been a staple in the cybersecurity realm for businesses handling credit card transactions. The Payment Card Industry Data Security Standard was developed to encourage and enhance payment card account data security. It helps define consistent security measures…
Read More -
Jan
24

Zero to hero: How zero-trust models protect against cyber-attacks
Perimeter-based security models were built for a world where corporate networks had clear boundaries—but that world no longer exists. Modern enterprises operate in hybrid environments with cloud services, remote workforces, and third-party integrations, creating countless entry points for attackers. The…
Read More -
Oct
12
How to configure the NCSC password list in AD
Passwords are one of the weakest links when it comes to ensuring that your environment is secure. Traditional user accounts and the associated passwords have long been the default security mechanism found in most environments. With the very advanced and…
Read More -
Sep
23
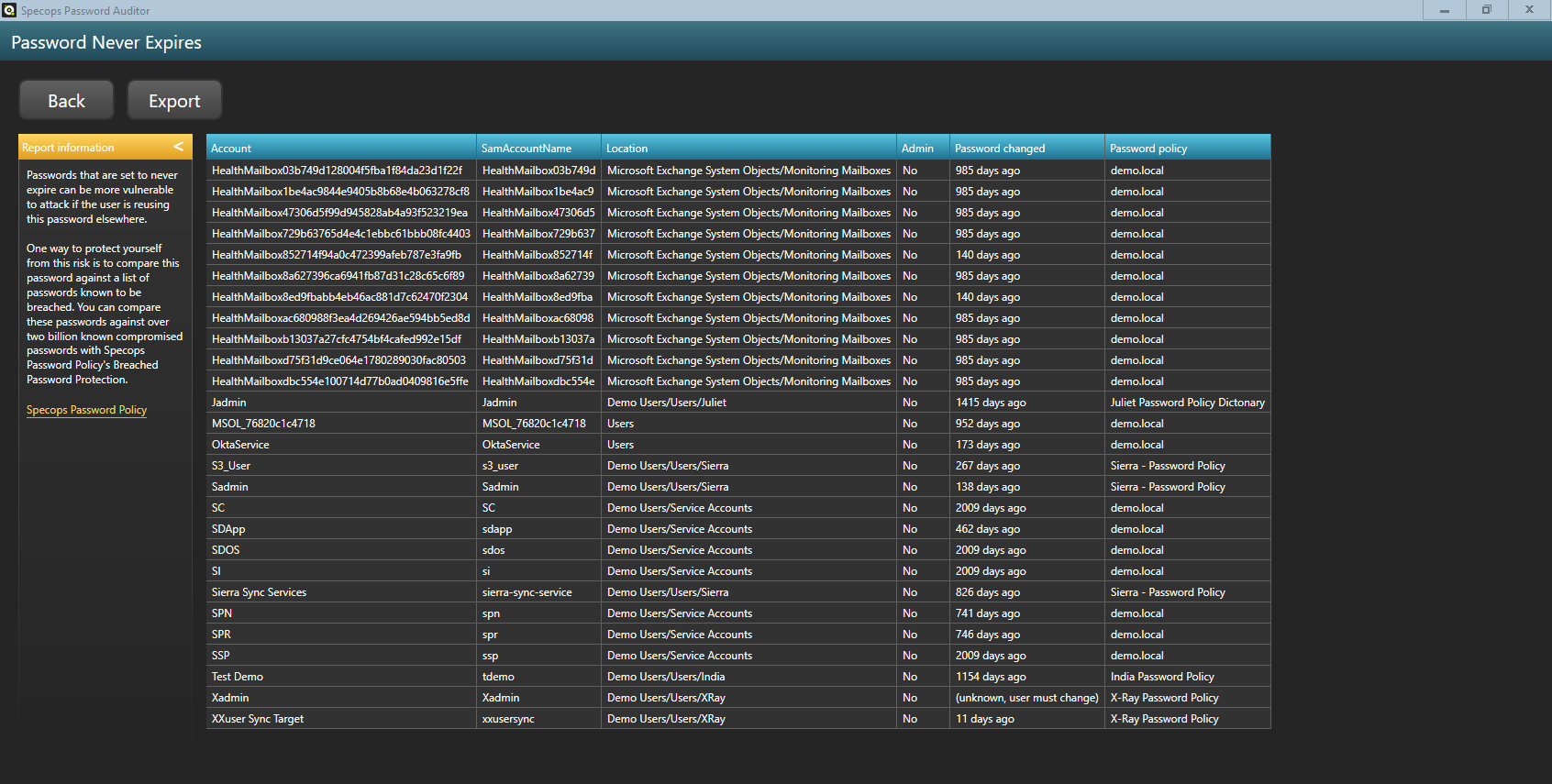
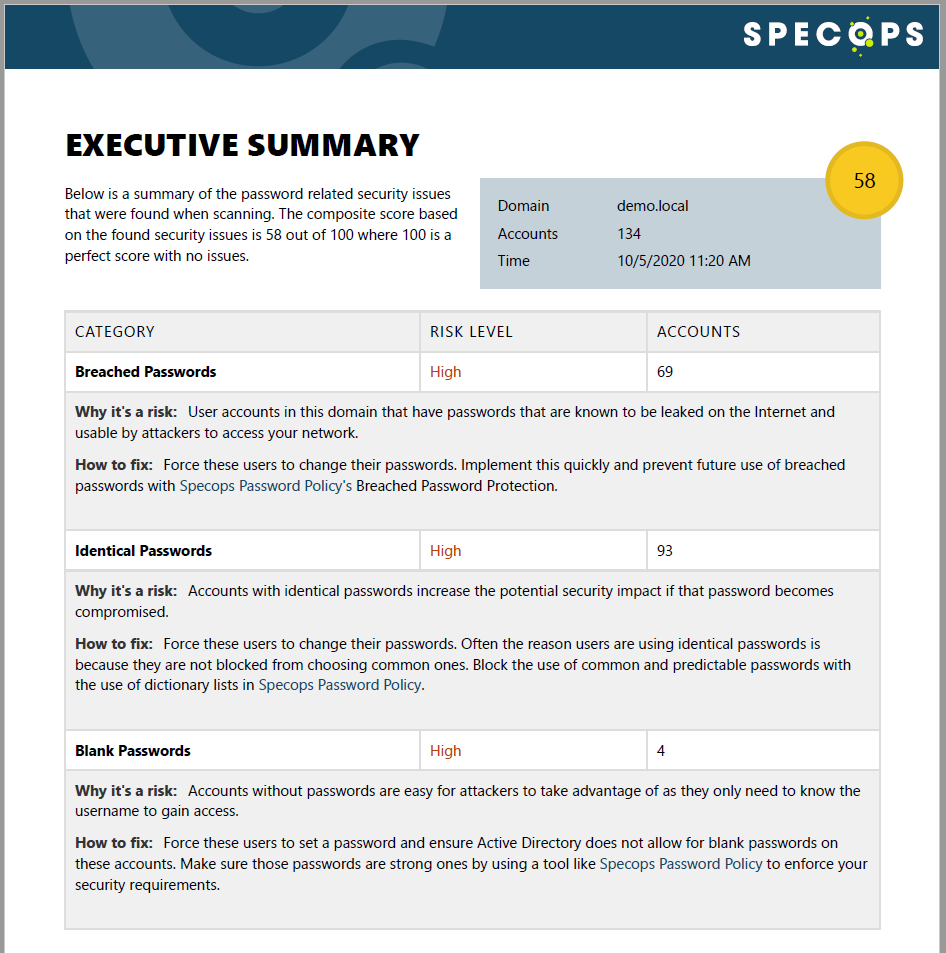
Finding Active Directory passwords set to never expire
Passwords set to never expire can be a security vulnerability for your network. Here is how to to find Active Directory (AD) passwords set to never expire. Some regulatory bodies require passwords to expire every 90 days, while others recommend…
Read More -
Jun
03

Which authentication tools are users most comfortable with?
Authentication is the first line of defense in any organization's cybersecurity strategy, but not all authentication tools offer the same level of security, convenience, or scalability. From traditional passwords to advanced biometric and adaptive authentication, businesses must carefully choose the…
Read More -
Nov
19

How to stop different types of password attacks
What makes users and organizations vulnerable to password attacks? A recent study indicates that user’s perceptions of password security might not always match reality. Many of us overestimate the benefits of including digits or special characters in our passwords, and…
Read More -
May
15
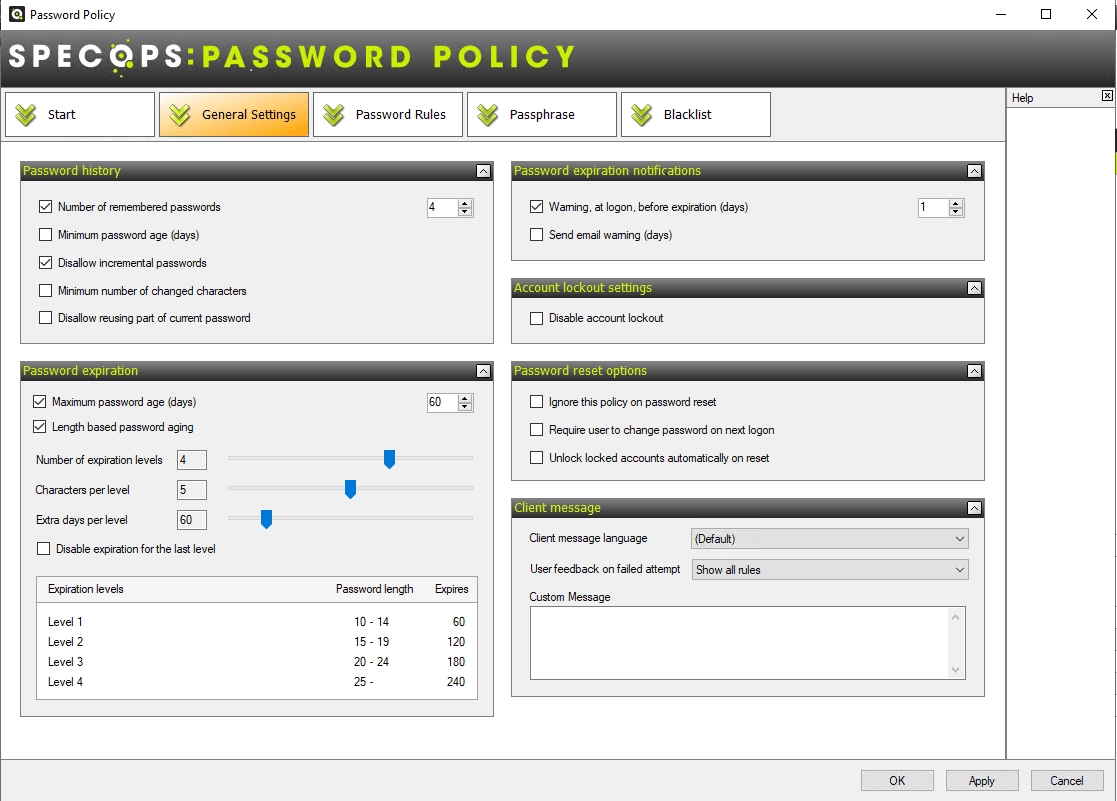
Password expiration policy best practice
An effective password policy is a balancing act – security is vital, but ineffective if usability suffers. Users already have too many passwords so NIST tells us to make life a little easier for them. For example, don’t force them…
Read More -
Apr
08

What is a password dictionary attack and how do password dictionary attacks exploit weak passwords
Imagine using the exact same lock and key for your front door as millions of others people. That's the reality of using weak or common passwords. In this blog, we'll explore how weak passwords are exploited via password dictionary attacks:…
Read More -
Jan
17

A smart alternative to SCCM
Are you looking for a smart and simple alternative to System Center Configuration Manager (SCCM)? Specops Deploy automates the installation of operating systems, software, and applications in your Microsoft Active Directory environment. Specops Deploy extends the functionality of Group Policy…
Read More -
May
26

Disallow special characters in Specops Password Policy
In this post, we will demonstrate how to disallow the use of special characters in passwords, in this case Swedish character, by using the “regular expression” setting in Specops Password Policy. Before getting started, ensure that you have installed the…
Read More

